Automating Trust as a Business Enabler: From Compliance Gate to Growth Engine
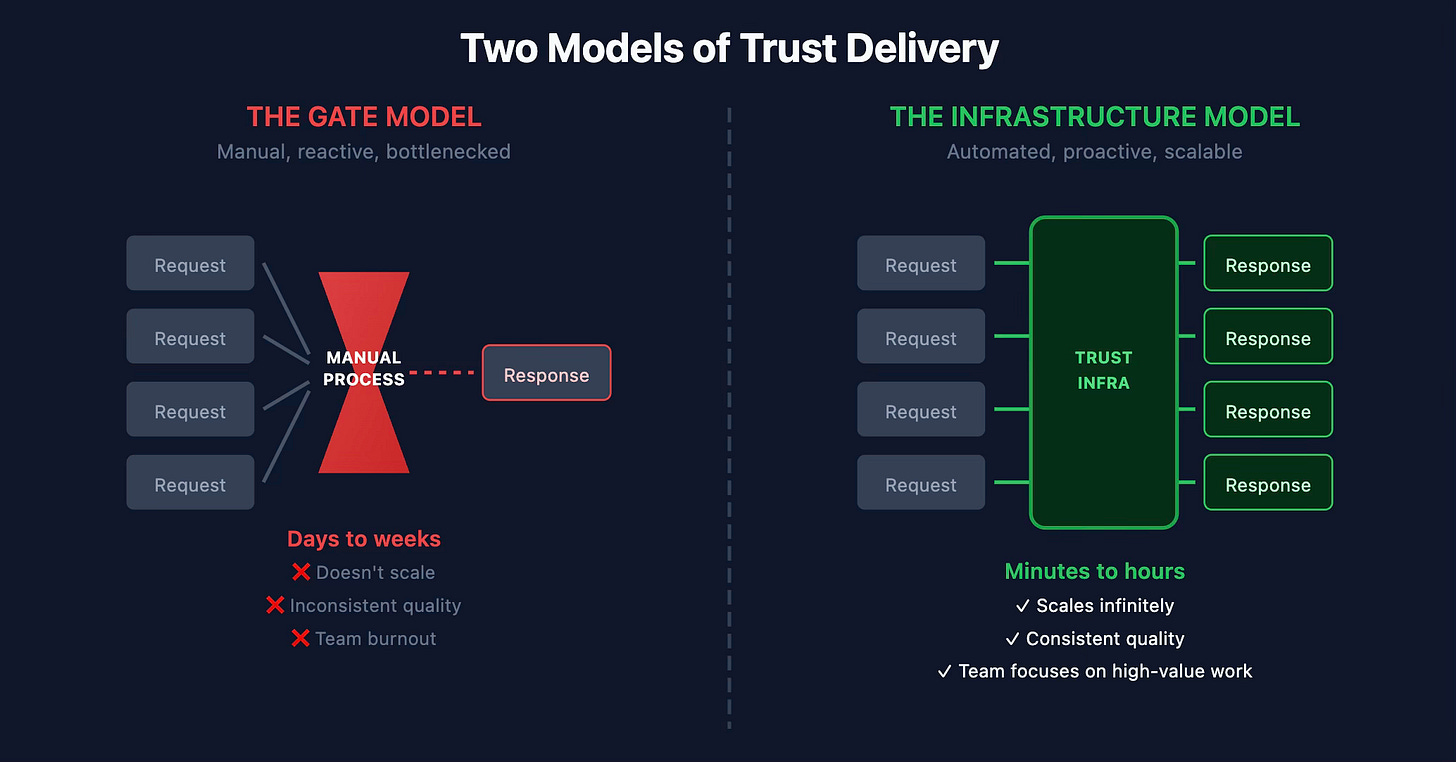
Compliance is either a gate that slows deals down or infrastructure that scales trust automatically. You're building one or the other.
In Part 1, we talked about using customer trust intelligence to shape your compliance roadmap. But knowing what to build is only half the challenge. The other half is delivering trust at scale without becoming a bottleneck.
This is where most GRC programs stall. They build the right capabilities, earn the certifications, develop the policies—and then bury it all behind manual processes that frustrate customers and drain internal resources.
The fix isn’t hiring more people to answer security questionnaires faster. It’s rethinking how trust gets delivered.
The Bottleneck Problem
Picture the typical enterprise sales cycle. A prospect is interested. They’ve seen the demo, liked the product, and have budget. Then procurement sends over a 300-question security questionnaire. Or they ask for your SOC 2 report. Or they want to schedule a call with your security team.
What happens next determines whether compliance is a gate or an enabler.
In the gate model, the request lands in someone’s inbox. Maybe it’s a GRC analyst, maybe it’s a sales engineer, maybe it’s whoever answered the last one. They dig through folders to find the latest documents. They copy-paste answers from previous questionnaires, hoping the information is still accurate. They wait for approvals. Days pass. The prospect’s enthusiasm cools. Competitors who respond faster gain an edge.
This model doesn’t scale. Every new customer means more manual work. Every certification you add means more documents to manage and more questions to answer. Growth becomes a burden on the compliance team instead of a victory.
The Infrastructure Model
The alternative is treating trust delivery as infrastructure—systems that serve customers automatically, consistently, and instantly.
This isn’t about replacing humans with bots. It’s about removing humans from tasks that don’t require human judgment, so they can focus on work that does.
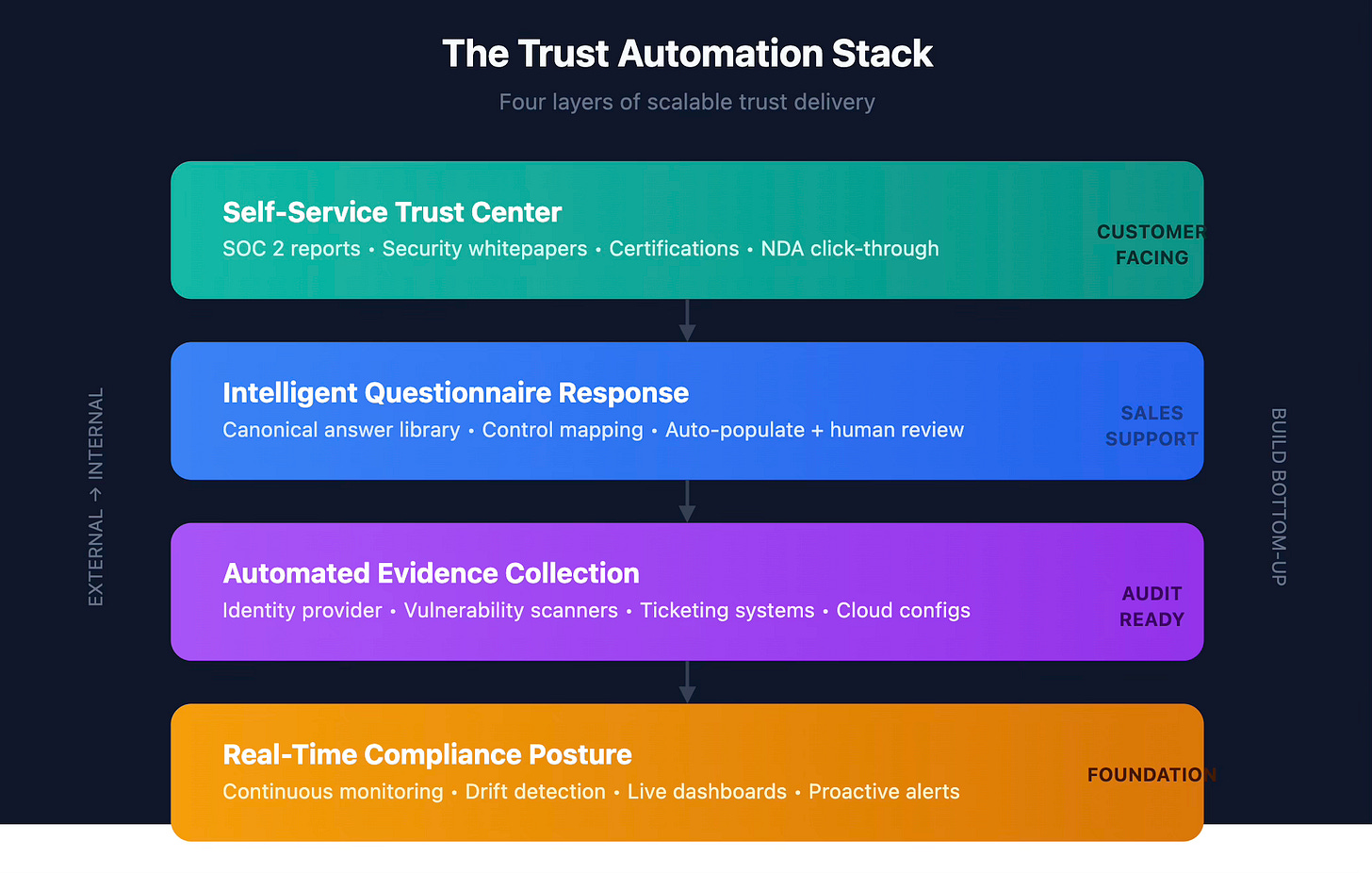
Self-service trust centers. Instead of emailing documents on request, publish them where customers can access them directly. SOC 2 reports, penetration test summaries, compliance certifications, security whitepapers—all available behind a simple NDA click-through. Prospects get what they need instantly. Your team doesn’t lift a finger.
Automated evidence collection. The bane of audit prep is chasing screenshots and exports from a dozen different systems. Automate that. Pull user access reviews from your identity provider. Pull vulnerability scan results from your security tools. Pull change management records from your ticketing system. When audit season arrives, the evidence is already there.
Real-time compliance posture. Point-in-time audits are table stakes. The next level is continuous monitoring—dashboards that show your current compliance state, flag drift before it becomes a finding, and give customers confidence that you’re not just compliant once a year but compliant right now.
Intelligent questionnaire response. Security questionnaires are repetitive by design. Most questions map to the same underlying controls. Build a knowledge base of your canonical answers, tagged by control and framework. Use it to auto-populate responses, then have humans review and customize. What took days now takes hours.
The GRC Engineering Mindset
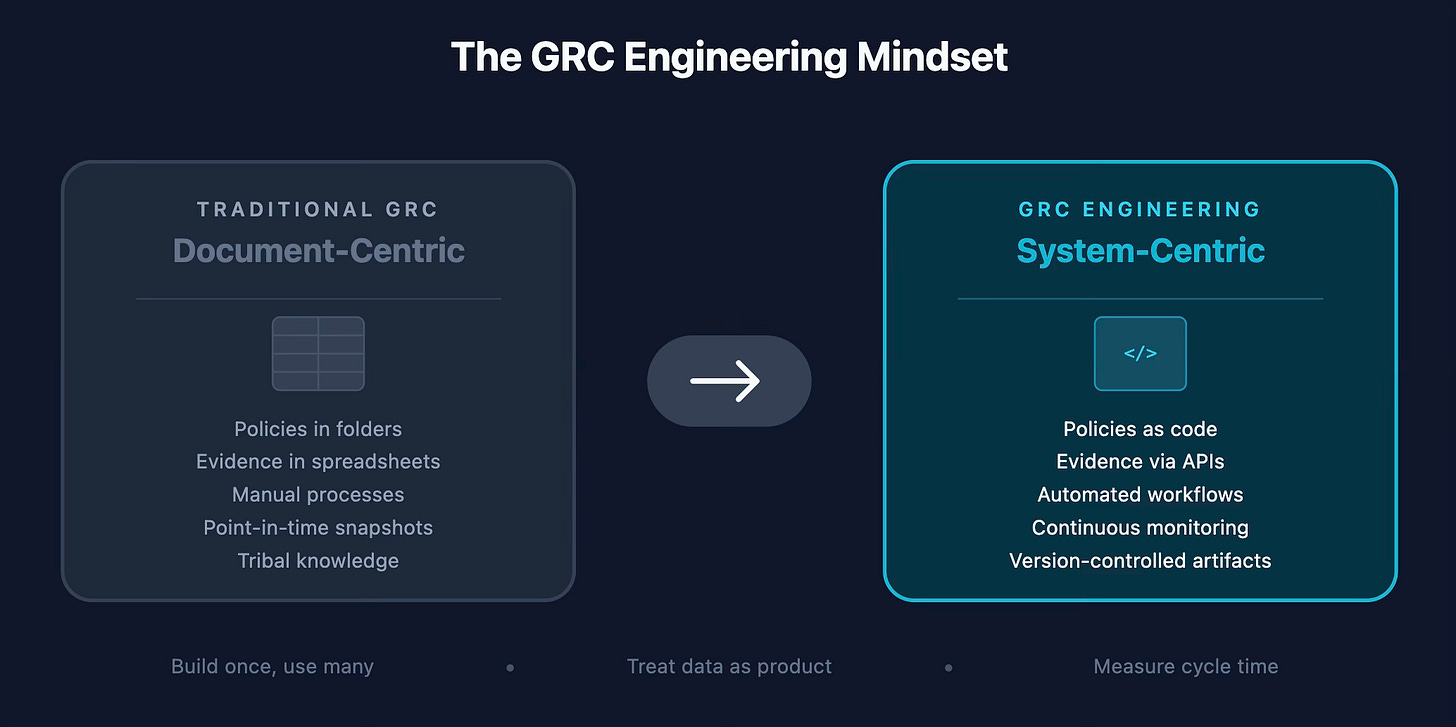
This shift requires a different way of thinking about compliance work. Traditional GRC is document-centric: policies, procedures, evidence binders, audit reports. Automated GRC is system-centric: integrations, workflows, data pipelines, APIs.
That doesn’t mean everyone on the GRC team needs to become a software engineer. But it does mean thinking like one:
Build once, use many times. Every time you manually generate a report or answer a question, ask whether that task could be automated. If you’ll do it more than twice, it’s worth systematizing.
Treat compliance data as a product. Your evidence, your control status, your certification records—these have consumers, both internal and external. Design how that data flows with the same care you’d design a customer-facing feature.
Version control your artifacts. Policies change. Controls evolve. Evidence gets updated. If you can’t trace what was true at a specific point in time, you’ll struggle in audits and incident response. Treat your compliance artifacts like code: versioned, reviewable, auditable.
Measure cycle time. How long does it take to respond to a security questionnaire? To produce evidence for an auditor? To onboard a new vendor? These are your compliance SLAs. Track them, set targets, and improve systematically.
The Business Case
Automation isn’t just about efficiency—though the efficiency gains are real. A GRC team that automates well can support 10x the customer base without 10x the headcount. That’s leverage.
But the bigger win is speed. In competitive deals, the vendor who delivers trust artifacts fastest often wins. When a prospect can self-serve your SOC 2 report at 10pm on a Sunday, you’re not waiting until Monday for someone to find it and email it over. When questionnaire responses come back in hours instead of weeks, you’re demonstrating operational maturity that reinforces the trust you’re trying to establish.
Speed also compounds internally. When evidence collection is automated, audit prep shrinks from a multi-week scramble to a routine process. When compliance posture is visible in real-time, you catch issues early instead of discovering them during the audit. When policies and controls are systematized, onboarding new team members takes days instead of months.
Getting Started
You don’t need to automate everything at once. Start with the highest-friction, highest-volume pain points:
If security questionnaires are killing you: Build a response library. Map your most common questions to canonical answers. Even a well-organized spreadsheet is a 10x improvement over starting from scratch each time.
If document requests are constant: Stand up a basic trust center. It can be as simple as a password-protected page with your key documents. Upgrade to a proper portal when volume justifies it.
If audit prep is a fire drill: Identify your most painful evidence items and automate those first. User access reviews and vulnerability scans are often quick wins because the data already exists in systems with APIs.
If you’re not sure where to start: Instrument what you have. Track how long things take. Follow the pain. The data will tell you where automation has the highest ROI.
Trust at Scale
The companies that win on trust in the next decade won’t be the ones with the most certifications on their website. They’ll be the ones who deliver trust effortlessly—to customers, to auditors, to partners, to regulators.
That requires treating compliance not as a periodic checkbox exercise, but as operational infrastructure. It requires building systems that scale. It requires the GRC Engineering mindset.
In Part 1, we talked about listening to customers to know what trust capabilities to build. In Part 2, we’ve covered how to deliver those capabilities at scale. Together, they form a model for GRC that isn’t just a cost center or a necessary evil—but a genuine competitive advantage.
The technology exists. The patterns are proven. The question is whether your compliance program is ready to make the shift.
This is Part 2 of a two-part series on building trust as a business enabler. Read Part 1: “Customer Trust as a Compass” for how to use sales partnership to shape your compliance roadmap.